Windows 10 End-of-Life: Your Complete Migration Strategy for 2026
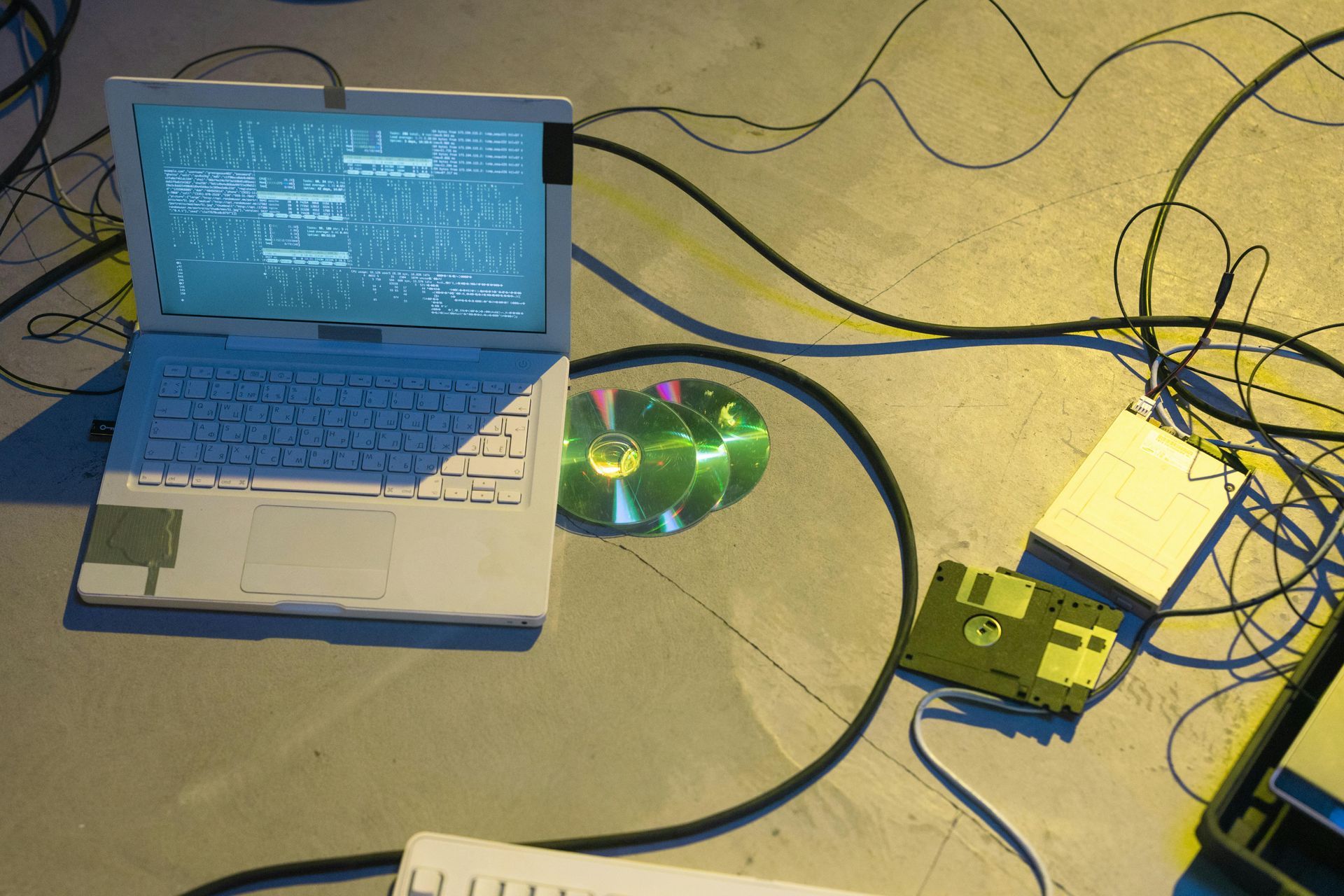
Windows 10 support officially ended in October 2025, leaving organisations running this operating system exposed to significant security vulnerabilities and compliance risks. Without security patches or updates from Microsoft, every unpatched system becomes a potential entry point for cyberattacks.
Understanding the Risks
Continuing with Windows 10 after end-of-life creates multiple problems. Unpatched security vulnerabilities accumulate over time, regulatory compliance becomes impossible to maintain, and cyber insurance policies may refuse coverage for breaches involving unsupported systems. The risk isn't theoretical—attackers specifically target organisations running outdated software because they know vulnerabilities won't be fixed.
Migration Options
Organisations have three primary paths forward. The most straightforward is upgrading to Windows 11, though this requires hardware compatibility checks as Windows 11 has stricter requirements than its predecessor. Alternatively, cloud-based virtual desktop solutions like Azure Virtual Desktop or altiaSRD provide modern desktop experiences without hardware refresh costs. For organisations with mixed requirements, a hybrid approach combining both strategies often works best.
Planning Your Migration
Successful migration requires methodical planning. Start with a comprehensive hardware audit to identify which devices meet Windows 11 requirements and which need replacement. Application compatibility testing is crucial—legacy applications may need updates or alternatives before migration. User training shouldn't be overlooked; whilst Windows 11 looks similar to Windows 10, interface changes can impact productivity if users aren't prepared.
Timeline matters significantly. Rushing migration creates problems, but delaying increases risk exposure. Most organisations need 3-6 months for complete migration, depending on size and complexity. Phased rollouts reduce risk by identifying issues before they impact the entire organisation.
Security During Transition
The migration period itself creates security challenges. Systems awaiting migration need enhanced monitoring and restricted access to sensitive data. Network segmentation can isolate legacy systems whilst migration proceeds. Enhanced endpoint protection provides additional security layers during the transition period.
Getting Support
Migration doesn't need to be overwhelming. Altiatech specialises in seamless OS migrations that protect security whilst maintaining productivity. Our team handles infrastructure assessment, compatibility testing, deployment, and ongoing support throughout the transition.
Ready to migrate from Windows 10?
Contact us today for a comprehensive migration assessment and strategy tailored to your organisation's needs.
📞 +44 (0)330 332 5482 | 📧 innovate@altiatech.com
Ready to move from ideas to delivery?
Whether you’re planning a cloud change, security uplift, cost governance initiative or a digital delivery programme, we can help you shape the scope and the right route to market.
Email:
innovate@altiatech.com or call
0330 332 5842 (Mon–Fri, 9am–5:30pm).
Main contact page: https://www.altiatech.com/contact













